Lonnie Stanley
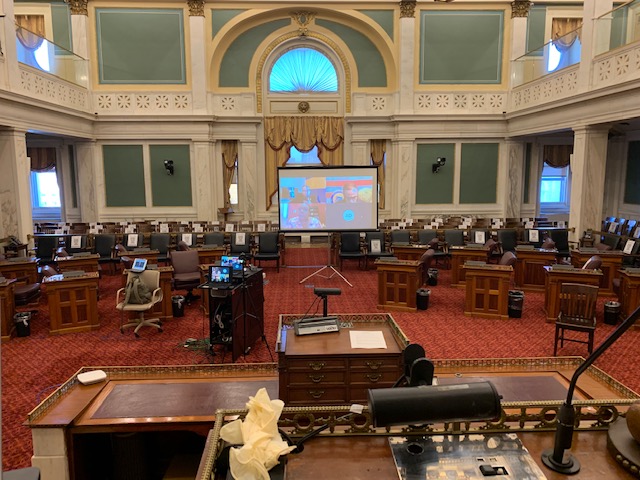
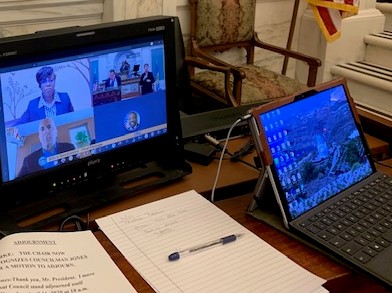
Philadelphia’s First Virtual Council Session

In light of the impacts of COVID-19, The Kimmel Group, Inc. was asked to design a solution for presenting the City of Philadelphia’s council sessions virtually.
As City Council’s technology provider for the last 20 years, we support over 200 users in 17 offices in City Hall and 11 district offices. We provide desktop, network and end-user support on a network managed by the City’s IT department.
Once it was clear that the pandemic may limit access to City Hall, we started looking at solutions.
Initially, we were working under the premise that the session would be a hybrid virtual session with nine members present (a quorum) and the remaining eight attending virtually.
After the “stay at home” and “social distancing” advisories from the State of Pennsylvania and the requirement that only essential employees come to work, our hybrid session edict quickly morphed into a fully virtual session after the official closing of City Hall to the public.
We were given a short amount of time to come up with a solution.
The requirements were straightforward.
A virtual Council session must:
- Allow all Council members to participate from home or their City Hall/district offices
- Allow Council members to hear each other, Council President and the Chief Clerk
- Provide for the stenographer to hear all speakers
- Provide access for residents with limited or no internet access
- Provide for the hearing impaired
- Support an unlimited number of public attendees (city population of 1.5M+)
- Provide public comment with the ability to put multiple callers on hold and to answer the calls in the order in which they are received. Also, when they call in, their voice needs to be heard by all Council members, the stenographer, the sign language interpreter and wherever the session is broadcast
After meeting with Council’s legal team and within two days, we developed a solution that met the above requirements. After a week of internal testing with Council’s legal team, we provided training for Council members and their legal assistants.
With less than three days to the first virtual session, we coordinated several mock sessions with all members attending virtually. Our final “dress rehearsal” simulated the real session with Council President and the Chief Clerk in City Hall Chambers and the rest connected remotely.
On April 2, 2020, the City of Philadelphia held it’s first Virtual Council Session with 16 of the 17 members participating remotely to approve an emergency $85.4M appropriation to battle COVID-19.
Council President Clarke was extremely pleased as were the other members and staff involved.
On May 18, 2020, the City of Philadelphia held it’s first Virtual Budget Hearing with close to 100 of the City’s leaders in virtual attendance. This work helped to enable Council to pass the budget before the June 30th deadline and also enabled Council to pass legislation that earmarked funds for COVID-related expenses.
After having produced over 50 virtual hearings using Microsoft Teams, we believe our solution positions the City of Philadelphia to continue to hold virtual council sessions throughout this pandemic and we look forward to supporting them in their efforts.
On a personal note, as a Philly native and son of former Philadelphia civil servant parents, it warms my heart to be able to provide such a solution after 30+ years in this industry, for the City I Love, The City of Brotherly and Sisterly Love.
– Lonnie Stanley, CEO @ The Kimmel Group, Inc. For more information, connect with me on LinkedIn or review our list of current projects.
Tech Tuesdays – Security Quick Tips
Tech Tuesdays – New Tech Toy
This holiday I bought myself an Amazon Echo Dot, the voice-activate cloud-connected personal assistant/speaker. My main purpose was to be able to listen to music in the study without having to connect my phone. Since I already had a Bluetooth speaker, I decided on the Dot which has a smaller footprint than the Echo. Right out of the box I was able to pair it to my speaker. After downloading the app to my phone, I was able to connect Alexa to my Amazon Music and Pandora apps. I later learned that it will play iHeart and TuneIn stations without signing in to those apps.
From that app I also configured my favorite sports teams, setup which news briefings I wanted to hear and defined my home address and work address so Alexa could provide traffic updates for my morning commute. After a brief voice training session, Alexa was ready to take my commands, the first of which was, “Alexa, Play Jeff Bradshaw station on Pandora” to which she responded, “Getting your Jeff Bradshaw station from Pandora” and then proceeded to play it. While reading in the study, I have asked Alexa for the weather forecast, what time Rogue One was playing at the theater and when my Eagles play again.
One of the best features Alexa has is the ability to view the history of the commands you send to it. In history, you also have the chance to tell Alexa if she did “what you wanted” or not. This surely helps to fine-tune the system.
Once I became comfortable with Alexa, I enabled Amazon purchasing. This can be tricky because Alexa will not distinguish between voices so anyone within range can place an order, however, I have setup a four digit confirmation code which only I know. I may share it with my wife this month.
The last cool thing I did with Alexa was connect it to my WeMo switches that power a few lights in my home. I gained plenty of cool points when we had friends over and I said to Alexa, “Alexa, turn the living room light on” and with a simple “OK”, she responded on cue.
I really enjoy my Amazon Echo Dot and look forward to expanding its features. My daughter gave me a book entitled, “The 189 Funniest Things to Ask Alexa!” I can’t wait to hear her responses. Until then, I will continue to use my go-to line after a hard day of work, “Alexa, Play Cranes in the Sky by Solange”
Enjoy,
Lonnie
Tech Tuesdays – New Year Tech Resolutions
The New Year is fast approaching. Many people will take this time to reflect and reminisce, flip or scroll through old photos and talk about the good days. There were some very memorable events this year that were picture perfect.
One that comes to mind was the Summer Olympics in the beautiful Rio de Janeiro, Brazil. All of the world’s greatest athletes competing in one city! There’s plenty of great shots: Michael Phelps winning his 28th Medal, Simone Manuel winning her first Gold Medal and yet another Simone, Simone Biles, winning Gold in the Individual All-Around. Another picture perfect moment was the first Super Moon in half a century! The Moon was the closet it’s been to the Earth this year and countless people took to the rooftops to snap a shot of it. On top of that there have been family vacations, holiday parties with friends and birthday parties with loved ones. All captured with the flash of a camera or smart phone!
Now that 2016 is coming to end, it is time to secure all of those wonderful memories. Make sure to back up all of your major devices. Push your photos to the cloud or save them manually onto an external hard drive. It only takes an accidentally dip in the pool with your phone in your pocket to lose a year’s worth of pictures.
Make sure to save all of those selfies!
2017 is right around the corner!
This week’s video from CNET gives you a full tech checklist to make sure you save the OLD and prepare for the NEW!
Enjoy,
Lonnie
TechTuesdays – Security is no laughing matter
This old clip from the Ellen Show is funny but sadly true. Someone was selling a book, re-branded as a place to store passwords. The company, which shall remain nameless, created the infomercial before actually creating a product to gauge consumer interest. Consumers were interested alright, interested in laughing.
Remembering passwords in our lives has become a tedious process. From bank accounts and online shopping sites to our email and social network logins, the task has become daunting. Life would be simple if we could use the same password for all our accounts but with data breaches like the one at Yahoo, having the same password or even security questions for accounts can be disastrous.
For personal passwords, apps like LastPass can be used to securely store your logins and passwords. The app even has a corporate edition which we have implemented for a client that wanted to share specific logins to their entire team. Lastpass has the ability to store personal passwords along with your “company” passwords. In addition, Lastpass supports multi-factor authentication (MFA) which grants users access to accounts only after providing several pieces of evidence such as a login and a code sent via text to their cellphone. In addition to Google and Microsoft, banking and credit card sites support MFA and the list grows daily. If your sites offer it, use it. It may prevent someone from accessing your accounts.
Security is also a major concern for businesses. In a survey released by KPMG covered in an Inc Magazine article, “A whopping 50%–half the CEOs polled–indicated that their firms are either not prepared, or only partially prepared, to deal with a major cyber event.” While the CEOs polled were from companies with at least $500M in revenue, it is clear that cyber-security is a pressing issue in 2016 for businesses as well.
If you run a business with less than $500M in revenue, a cyber breach may be more devastating than to a larger firm. It may result in the loss of revenue, reputation or worse, customers. Security in business is everyone’s concern and cyber-security is no different. Companies need to adopt polices and procedures to ensure that all employees are aware of best practices to minimize the threat posed by hackers and competitors looking to do harm.
Below is a partial list (created by by Joseph Steinberg CEO, SecureMySocial) that provides tips on securing your company from cyber attacks. For the complete list, please click here
Enjoy,
Lonnie
CyberSafety Tips
- – Ensure awareness – help employees understand that they are targets
- – Offer basic information-security training
- – Backup Often
- – Encrypt – especially laptops
- – Use a proper password policy
- – Devise, implement, and enforce social media policies
- – Address personal device risks
TechTuesdays – Social Media and the Job Search
As college graduation dates near, the frantic search for a job has begun on college campuses across the country. Students are fine-tuning their resume’s, looking for that best-fit position, researching employers and attending countless interviews. I recall those days fondly. I would spend hours pouring through the paper or checking the bulletin boards at school. Technology sure has changed the game for today’s graduates in ways that are good and some that are not so good.
Today’s employers rely on more than career web sites or college career centers to seek candidates. According to a 2015 survey of Human Resource professionals by the Society for Human Resource Management, “82 percent of organizations said recruiting passive job candidates is top reason organizations use social media for recruitment”. Sites like LinkedIn, Facebook and Twitter have been used to recruit candidates. According to the survey, LinkedIn was the most popular choice among respondents at 93%. This represents the “good” use of social media during the job search. If your profile matches the needs of the employer, they may find you before you find them.
On the not-so-good side, a candidate’s social media profile can expose a potential employer to the less-than-desirable persona that most likely will not be selected for a position. While employers are searching for a match, they are also screening profiles for reasons including: “obtaining more information about the applicant than provided in a resume (61 percent)” and “easily verifying information from a resume (50 percent).” See full article here
If a candidate isn’t tech-savvy enough (or smart enough) to protect their posts, perhaps they aren’t the best candidate after all. In today’s environment, the wrong post could mean the rescinding of a job offer or in some cases, termination after hiring. During my college job search days, my main concern was making sure my apartment answering machine’s outgoing message was changed to reflect my more “professional” side. I didn’t even have cell phone voice mail to worry about.
Technology certainly has made the job search easier for today’s graduates but with that ease comes greater responsibilities and greater risks.
This week’s TechTuesday video from snagajob discusses the Do’s and Don’ts of Social Media as it relates to the job search.
After viewing, ask yourself, if a potential employer looked you up on social media, what would they find?
Much success,
Lonnie
TechTuesdays – Crowds in the Cloud
The recent cinematic release of Don Cheadle’s biopic of Jazz legend Miles Davis, Miles Ahead has brought to light the concept of Crowdfunding. Cheadle used web site Indiegogo to initially fund the project, raising over $300,000. Investors were offered perks ranging from mugs, tee-shirts, hoodies, albums or opportunities to attend the filming or editing of the movie as a guest of Mr. Cheadle. Some were even offered the chance to have their name listed in the credits as an Associate Producer. The “Crowd” was anyone interested in helping Mr. Cheadle realize his dream of bringing this movie to the masses. He was able to reach beyond his network of friends and family to Miles Davis and Jazz fans throughout the world who were interested in seeing this project come to fruition. Not only were they able to show their support, they were able to financially back it with amounts ranging from $5 to $25,000.
With sites such as Kickstarter, GoFundMe and Indiegogo, anyone can use crowds in the cloud to fund a project, a show, a new invention or even a real estate deal. For the crowd of potential investors, there is an opportunity to get in on the ground level of a successful product or they can simply provide financial support for worthy causes.
The global crowdfunding industry was predicted to grow to approximately $34.4 Billion (yes, with a “B”) by the end of 2015 according to an industry report. 2016 looks to continue that trend. However, the Crowd can be used for more than just funding. With cloud technology, people all over the world can participate in virtual think-tanks to develop cures for disease or ways to eliminate poverty. It’s not always about the money. The original term, Crowdsourcing (or crowd outsourcing) is defined by Websters as “the practice of obtaining needed services, ideas, or content by soliciting contributions from a large group of people and especially from the online community rather than from traditional employees or suppliers”. Crowdfunding is just one form of Crowdsourcing. As this week’s TechTuesday video explains, the Crowd (and the cloud) can be used in so many ways to make our world a better place.
I hesitated when the Miles Ahead Indiegogo campaign started and I regret that but next time, I will make sure I participate. I’m sure you have received at least one invitation to join a funding campaign. After viewing this week’s video, I hope you will be more informed and can feel empowered to get involved.
Pardon me as I go check on my daughter’s GoFundMe campaign. Her dance group is raising funds for their benefit recital. They are close to reaching their goal and I was glad to be a part of it.
Enjoy,
Lonnie
TechTuesdays – Virtual Reality & Sports
Last week, during golf’s Masters Tournament, viewers were provided an enhanced viewing experience. Those with 4K televisions and service were able to view Amen Corner (Holes 11, 12, and 13) via the first tournament broadcasted in 4K video. But even more impressive was the debut of another next-gen viewing experience, Virtual- Reality (VR). VR content developer, NextVR “installed 360-degree cameras on tee-boxes and greens at popular holes 6 and 16, where spectators historically gather” according to a CNET article. These tech advancements are major changes for The Masters which has been reluctant to change over its 80+ year history. VR at sporting events may become the norm as NextVR continues to provide coverage for other sports such as NBA, NHL, NASCAR, Premier League Soccer, golf and boxing. NextVR signed a 5-year deal with Fox Sports to cover a host of events which may include NFL and Major League Baseball as well. The future of live-streaming is here now and for sports fans, it’s 360-degree immersive experience will surely come close to actually “being there”. With investments from the likes of Comcast, Time Warner and Dick Clark Productions totaling $30M, the future of VR looks bright.
This week on TechTuesdays, we’ll receive an explanation of Virtual-Reality from one of my favorite YouTube techies, Marques Brownlee.
Enjoy,
Lonnie
TechTuesdays
TechTuesdays – Public Wi-Fi Safety
You are probably reading this post on your phone or tablet via Wi-Fi. With the soaring costs of mobile data, most people rely on Wi-Fi for social media updates and streaming music. Some even keep their phones on Wi-Fi wherever they go to keep data costs down. The problem is this; you never know what open Wi-Fi networks you are connected to and who else is on those networks. Even known networks cannot be trusted.
In a survey referenced by security software developer Kaspersky “70% of tablet owners and 53% of smartphone/mobile phone owners stated that they use public Wi-Fi hotspots”. Due to the nature of Public Wi-Fi networks, any data sent can be intercepted such as personal information, financial transactions or web site logins and passwords. Those without effective anti-virus and anti-malware software are extremely vulnerable. (view our previous TechTuesday video on Malware)
This week on TechTuesdays, we will share a video that explains how public Wi-Fi works.
After reviewing, please return and review the list of wireless safety tips listed below: (adopted from Kaspersky’s list)
Enjoy,
Lonnie
Wi-Fi Safety Tips
- – Be vigilant at all times….Wi-Fi by design is insecure
- – Treat all Wi-Fi links with suspicion. Someone may be spoofing a legitimate establishment’s Wi-Fi name
- – Verify all public Wi-Fi networks with the establishment’s employees to ensure legitimacy
- – Avoid websites where personal information can be compromised such as social media, online banking or shopping
- – Consider using your cell phone’s hotspot feature to connect your tablet or laptop
- – Protect all devices with up-to-date anti-virus and anti-malware software
- – Use VPN connections when you can to provide a buffer between you and cybercriminals
- – Turn off your device’s Wi-Fi connection when no longer in use. Enable as needed.